Detecting and analyzing border gateway protocol blackholing activity - Farasat - 2021 - International Journal of Network Management - Wiley Online Library

Analysis of Effects of BGP Black Hole Routing on a Network Like the NIPRNET: Kleffman, Michael D.: 9781249586630: Amazon.com: Books
Static and Black Hole Routing :: Chapter 15. Routing Protocol Protection :: Part VI: Managing Access Through Routers :: Router firewall security :: Networking :: eTutorials.org
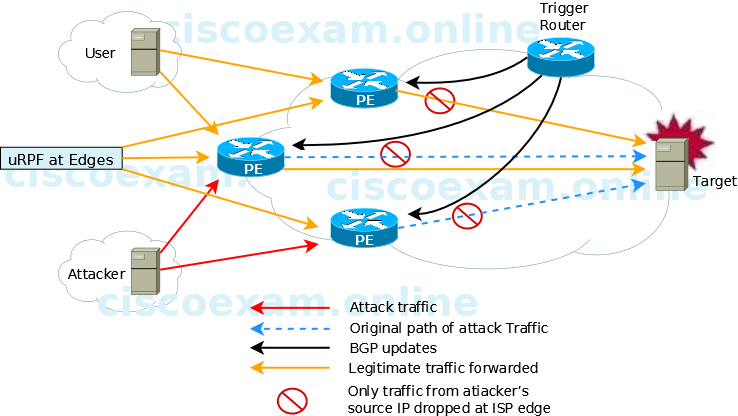
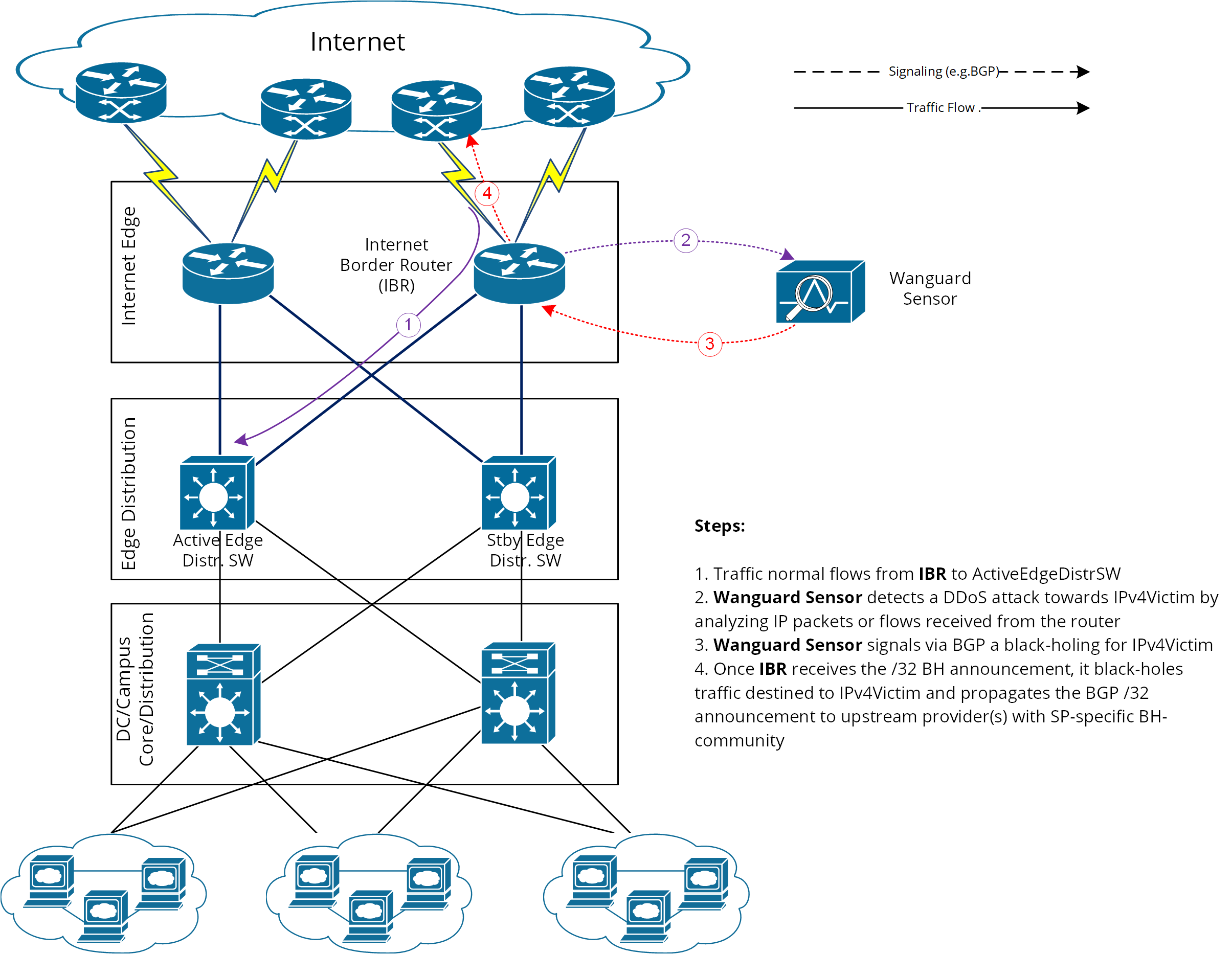
When implementing source-based remote-triggered black hole filtering, which two configurations are required on the edge routers that are not the signaling router?